For school leaders, cybersecurity now plays a central role in protecting students and staff, and ensuring school operations run smoothly. As more learning shifts online and schools rely on digital platforms every day, understanding who and what is accessing your systems has become critical. This is where identity comes in.
Identity sits at the heart of modern cybersecurity. When identity is well managed, schools reduce their exposure to cyber threats, protect sensitive information, and keep learning environments running smoothly. When it is not, attackers can gain access simply by pretending to be someone they are not. This makes identity one of the most important areas for school leaders to understand and strengthen.
This is why identity matters, and why taking the time to understand it is so important for school leaders. When you grasp how identity works, you can make stronger decisions, support your staff better, and reduce the chance of disruptions that affect learning.
Understanding identity in a school setting
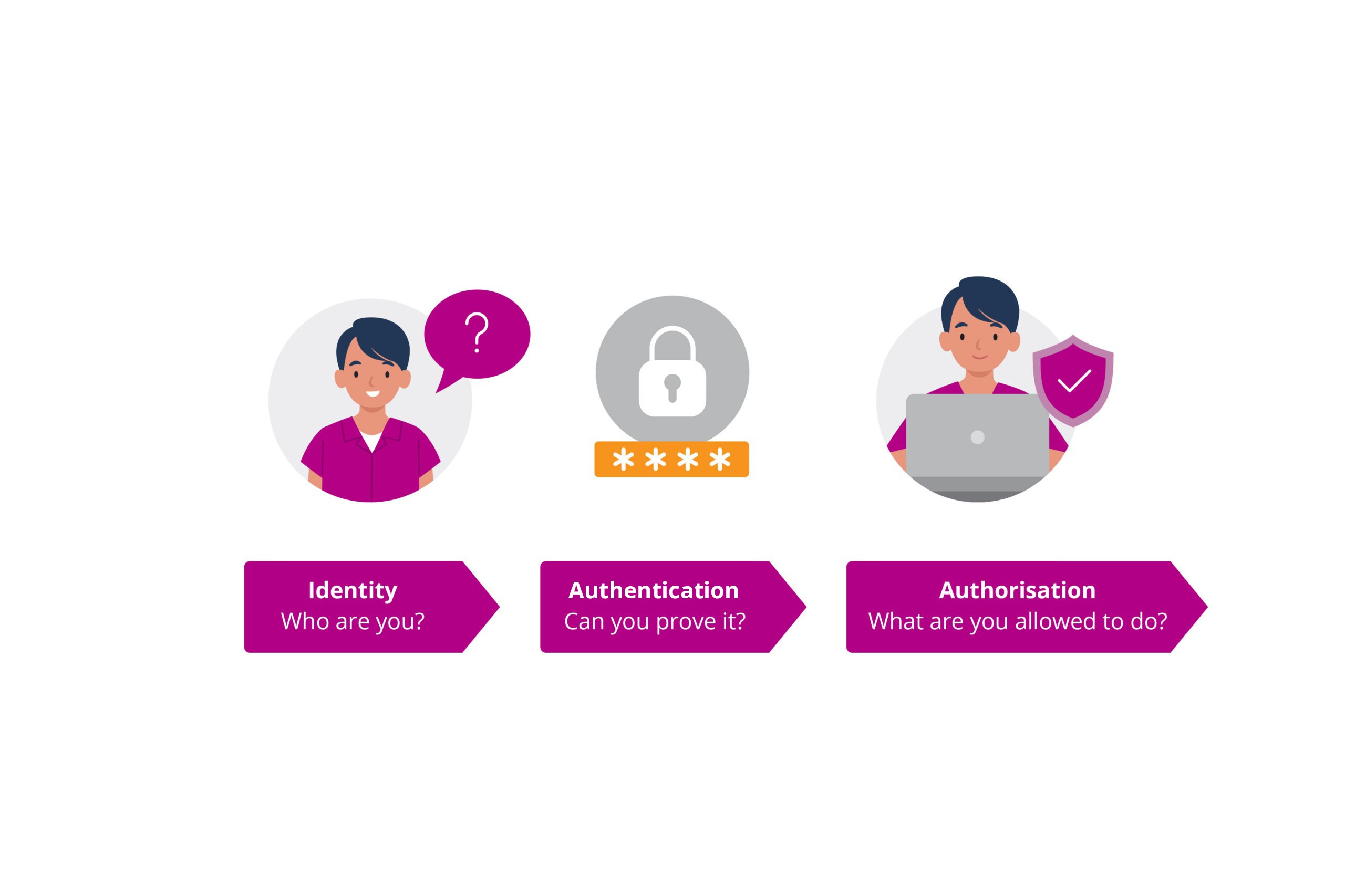
In digital systems, identity acts like a passport. It uniquely represents a person, device, or service, answering the question, “Who are you?” A teacher’s login, a student’s Google profile, or a certificate that verifies a school Chromebook are all examples of identity at work.
Once a system recognises an identity, it can start making decisions about how that person or device should be treated. That initial recognition is the foundation for securely accessing all kinds of school technology.
Proving identity through authentication
Claiming an identity is one thing, but proving it is another. Authentication is the process of verifying that someone really is who they say they are. In a school environment, this might be entering a password, responding to a two-factor authentication prompt, scanning a fingerprint, or a device using its certificate to prove it is school-owned.
Stronger authentication makes it harder for attackers to break in, even if they manage to steal or guess a username. In practice, this means schools need reliable ways to verify both the person and the device before granting access to their network. N4L’s Secure Access service helps schools do this by checking user and device identity at the point of connection, adding an important layer of protection.
Deciding what each identity can do
Once identity is confirmed and authenticated, systems need to determine what that person or device is allowed to access. This process is known as authorisation.
A principal might access financial systems, a teacher might see only their class data, and a student might be limited to learning tools. Even devices have authorisation rules that determine which networks or applications they can use. These access rules prevent accidental misuse and limit damage if an account is ever compromised.
How schools manage identities every day
In digital systems, people and devices each have their own identities. A user identity belongs to a person, such as a teacher or student, while a device identity belongs to items like laptops, tablets, or printers. Systems treat these identities separately because both the person and the device need to be trusted before access is granted.
Most schools rely on identity and access management (IAM) systems such as Google Workspace or Microsoft Entra ID to manage the full lifecycle of identities. For example, when someone joins the school, an identity is created for them via the school user directory.
These systems also manage device identities, passwords, access policies, and security controls like multi-factor authentication. Keeping identities updated and consistent is a major part of maintaining a secure school environment.
N4L’s systems also integrate with school user directories, so we can recognise users and apply the right access and filtering settings. One example of this is the Cloud Identity Engine (CIE), which schools connect to as part of their Managed Network upgrade. Completing this integration makes it easier for schools to adopt new functionality in the future.
Why attackers target identity
Most cyber incidents begin with compromised identity. Phishing emails, credential theft, and session hijacking all aim to trick people into handing over their access. If an attacker can successfully impersonate a teacher or administrator, they can bypass many traditional defences.
Strong identity protection reduces these risks significantly. Services like N4L’s Secure Access support schools by ensuring network access is tied to verified users and school-owned devices. Once a device is recognised, the network can apply the right settings automatically, helping administrators understand who is accessing the network and maintain appropriate controls.
How identity supports safer learning environments
Understanding identity isn’t about becoming a cybersecurity expert – it’s about making sure your school stays safe, resilient, and able to focus on teaching and learning. When you have confidence that the right people on the right devices are accessing your systems, everything else becomes easier: protecting student data, supporting staff, meeting compliance requirements, and reducing the risk of costly disruptions. Strong identity practices give school leaders peace of mind that the digital environment is more secure, reliable, and set up to support great learning outcomes.
Disclaimer: AI-assisted content. Human-reviewed and edited.
If you’d like to hear more from N4L, or see more blogs like this, why not subscribe?

